Ethical hacking is the process of finding flaws in computer networks in order to exploit them so that they may be corrected afterward. Hackers employ a variety of ways to discover risks and, as a result, improve the device’s security. A hacking operating system is the most basic tool that any hacker needs. The Linux kernel is usually used as the foundation for hacking operating systems.
The following are the operating systems that are used for ethical hacking and penetration testing.
1. Kali Linux

img source: cyberpunk.rs
Kali Linux is a Linux distribution that comes pre-installed and is based on the Linux kernel. Kali Linux is a Debian-based, open-source Linux system aimed at different data security activities such as testing process, security research, forensic investigation, and reverse engineering. Become a certified ethical hacker by gaining all the skills hands-on with this Ethical Hacking Training from Intellipaat.
Features:
- Kali Linux is free of charge and includes over 600 penetration tools, including Wireshark, Crunch, Nmap, and Aircrack-ng.
- Kali Linux utilities support many languages, allowing users to work in their preferred language.
- The Kali Linux code repository can only be accessed by a small number of trustworthy persons.
- FHS is followed by Kali Linux to make it easier to find libraries, support files, and other files.
2. Parrot Security OS
Parrot is a global community of developers and security experts that collaborate to create a common framework of tools to make their jobs simpler, more standardized, and safer. Parrot OS, Parrot Security’s main offering, is a Debian-based GNU/Linux distribution that prioritizes security and privacy.
Features:
- It’s accessible as a lightweight program that uses few resources.
- You are free to view and modify the source code in any manner you choose.
- Expert assistance is available to assist you with cybersecurity.
- The architecture for this hacker OS is decentralized, with specialized CDNs (Content Distribution Network).
- This operating system can be shared with anyone.
3. BackBox

img source: miloserdov.org
BackBox is not just an operating system. It is a Ubuntu-based Free Open Software Community dedicated to creating information security in the IT environment and making it safer and more efficient. All of this was accomplished using only Free Open Source Software, showcasing the Community’s potential and strength.
Features:
- It is best in both speed and performance.
- This hacker os has a user-friendly desktop interface.
- It aids you in computer forensic investigation, risk analysis, and other similar tasks.
- To prevent redundancy, develop with precision.
- It uses the bare minimum of your system’s resources.
- Allows you to mimic a software or network assault.
4. DEFT Linux
DEFT (Digital Evidence & Forensic Toolkit) is a customized Ubuntu live Linux CD distribution. It’s a user-friendly system with great hardware recognition and some of the top open-source response and recovery and computer forensics apps.
Features:
- There are open-source programs for inquiry in this environment.
- To execute programs in safe mode, an integrity check is performed before the start of each program.
- This ensures that the examiner’s tools are running securely. This rules out any malware-related harm to the binaries before.
- It has a hardware detecting feature.
- It provides a choice of main view packages as well as all monitored packages.
5. Black Arch
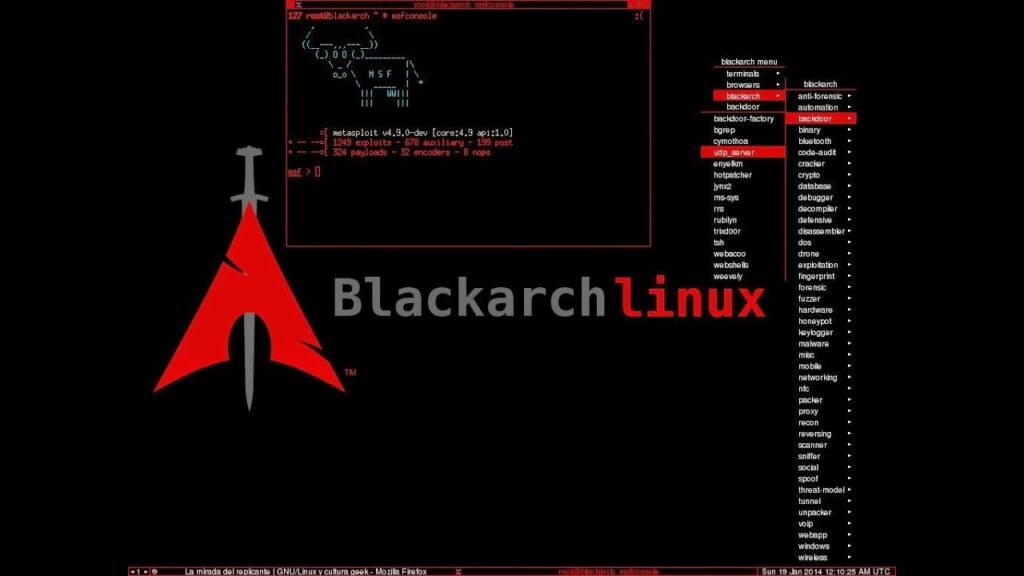
img source: youtube.com
BlackArch is an Arch Linux-based penetration testing distro with a huge number of cybersecurity tools. It’s an open-source distribution designed specifically for security researchers and penetration testers.
Features:
- It has various window managers and live ISO (International Organization for Standardization).
- This operating system can be operated on a low-resource machine.
- Supports many architectures.
- The installer may be made from scratch.
- There are 2707 tools in the repository.
6. Archstrike
ArchStrike is an Arch Linux-based distro for security professionals and researchers. ArchStrike is a security software repository that is available in Openbox and Minimal 64-bit versions. The Openbox window manager is used by ArchStrike to offer a live desktop environment. To keep packages up to date, it adheres to Arch Linux OS guidelines. Pen testing and security layering may both be done in this environment. You can install or uninstall it without difficulty.
Features:
- ArchStrike comes with approximately 5000 packages, which cover virtually everything you’ll need in a variety of areas.
- It provides a choice of main view packages as well as all monitored packages.
- Open-source apps for inquiry are available in this environment.
- It has a hardware detecting feature.
7. Fedora Security Lab

img source: fedoramagazine.org
The Fedora Security Lab offers a secure hardware platform for educational institutions and other companies to work on security audits, forensics, system recovery, and education information security techniques. A community of security testers and engineers keeps the spin going.
Features:
- It’s a Linux distribution based on Fedora that operates on both 32-bit and 64-bit systems.
- It includes a customized menu with all of the instructions necessary to follow the proper test path.
- This program may create a Live USB drive (a full operating system that can be booted)
- You have the option of saving your test results indefinitely.
- It produces a live image that allows you to install applications while the computer is operating.
8. Dracos Linux
Dracos Linux is one of the greatest hacker operating systems available. Dracos Linux is a free-sourced Linux operating system developed in Indonesia, based on Linux From Scratch and protected by the GNU General Public License v3. 0. Hundreds of people use Dracos Linux in Arm for hydraulic pen testing, forensics, and reverse engineering.
Features:
- This platform is open to everyone to study, alter, and share.
- Dracos Linux is a quick operating system for malware investigation.
- This hacking OS does not gather any of your personal information.
- It enables ethical hackers to do information security with ease.
9. Samurai Web Testing Framework
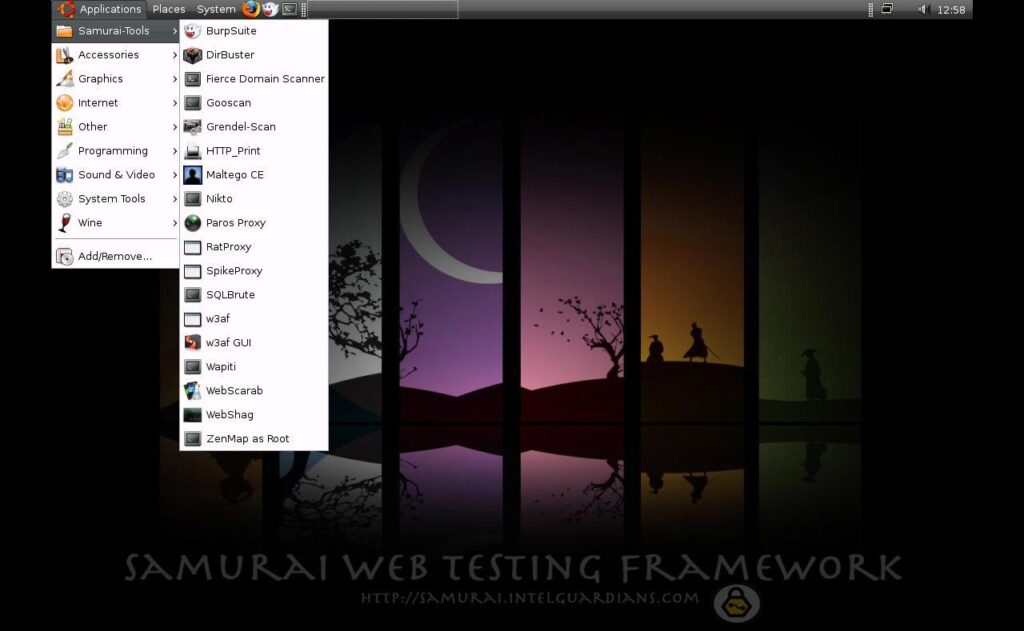
img source: securityonline.info
SamuraiWTF (Online Train and Test Platform) is a pre-configured virtual server that runs on VirtualBox and VMWare and serves as a web pen-testing and training environment.
Features:
- It is an open project that specializes in website attacks.
- It comes ready to use in a web pen-testing scenario.
- Features that can be utilized to concentrate on the website’s assault.
- WebScarab (an online security application development tool) and proxy (a web proxy server) are among the technologies included.
10. Caine
CAINE is an Ubuntu-based software that gives a user interface to a comprehensive forensic environment. As just a plugin, this operating system may be incorporated into current software tools. It is one of the greatest hacking operating systems since it pulls a chronology from RAM efficiently.
Features:
- It’s a free initiative.
- All devices are put into read-only mode by CAINE.
- This operating system may be integrated into current software.
- During the digital inquiry, an environment aids the digital investigator.
- CAINE’s characteristics may be customized.
- It has an easy-to-use operating system.



